Cyber security companies provided an invaluable resource for a wide range of enterprises throughout the United States. In today’s highly connected world, there are numerous risks related to sophisticated IT systems that often contain incredibly important information. As such, these businesses once they are established, enjoy a significant degree of economic stability given that they remain in demand for businesses of all sizes. When we develop a cyber security IT firm business plan, one of the things that we focus very heavily on is their viability. From a financial standpoint, individuals and companies that partner with these types of businesses, fully appreciate the ongoing demand in need for the services in any economic climate. The risk profile associated with this type of enterprise is relatively low once they are fully established given that they produce highly recurring streams of revenue from their operations.
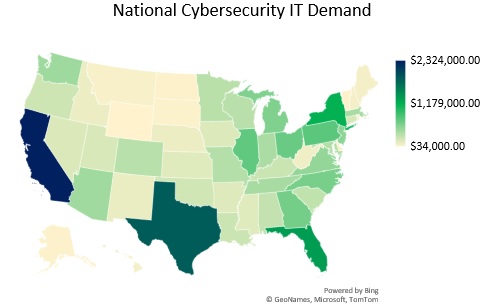
When we develop a cyber security IT firm business plan, we first conduct an extensive amount of market research regarding the market in which the business is located. It should be noted that we can complete this analysis in a dual capacity by not only focusing on acquiring clients on a regional basis but on a national basis as well. Through the power of the Internet, cyber security businesses are able to work with national level clients, especially as it relates to certain services specific for auditing and monitoring. When we take a regional approach for the market research, we examine the number of companies within the market that require these services spanning financial service companies, healthcare businesses, technology development, firms, as well as professional service businesses. This allows us to form both the total addressable market as well as the service obtainable market. We also conduct an extensive amount of competitive analysis to see how many other enterprises are operating within a similar capacity.
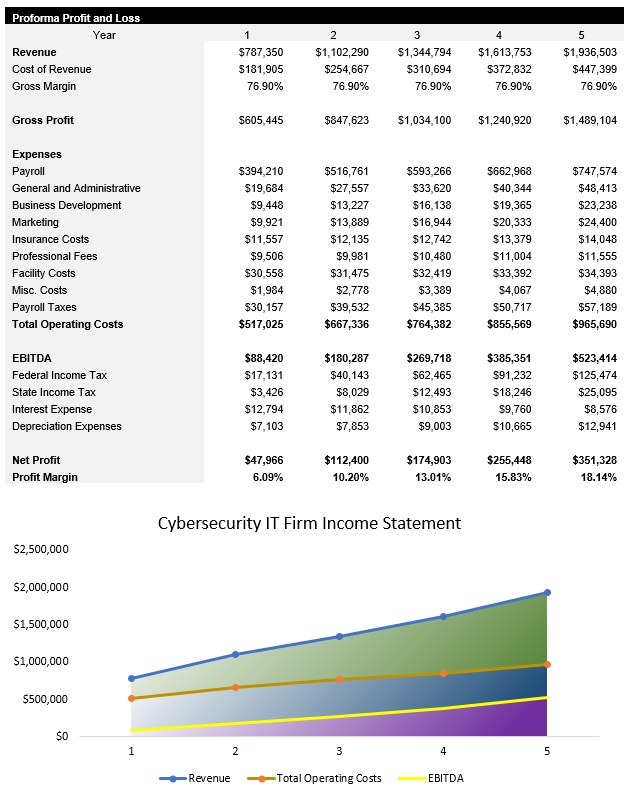
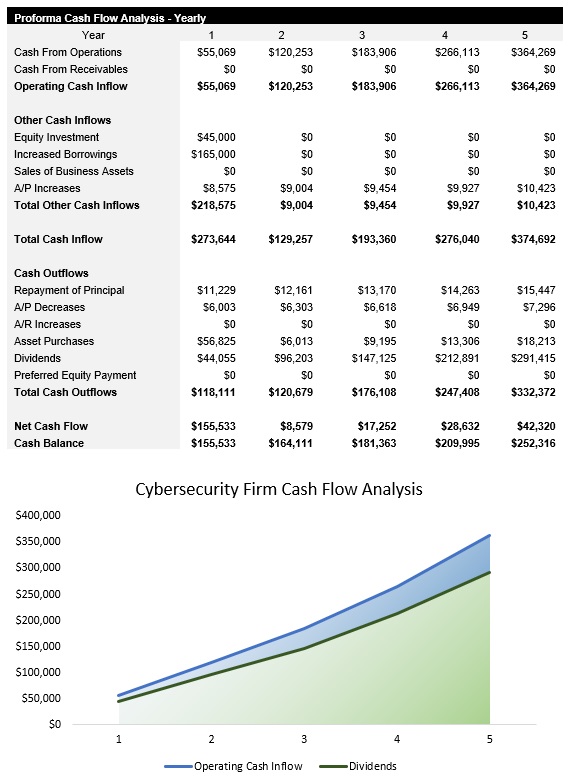
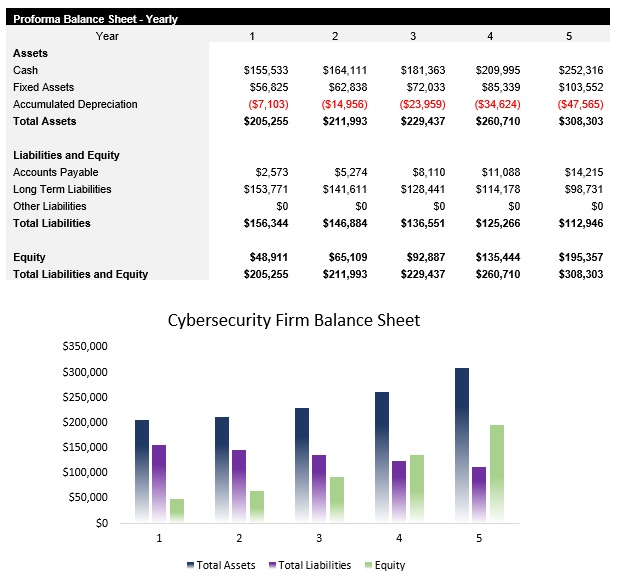
Once we establish the market size, on both a regional basis and national basis, we then focus on developing the cyber security IT firm financial model. In every plan that we complete, this includes a five-year profit and loss statement, cash flow analysis, common size income statement, balance sheet, breakeven analysis, asset acquisition analysis, as well as a DSCR analysis if it is applicable. We also create a revenue profile that showcases the income that is produced from each type of service rendered by a cyber security focused IT firm.
The third phase of developing this type of business plan is focused on the operations of the business. This includes discussing the specialized types of labor that will need to be hired in order to provide the wide range of services that are part and parcel of a cyber security firm. We also discussed the use of certain procedures and protocols in the event that a client has a significant emergency. The hiring plan as well as other matters related to human resources is included in this part of the analysis as well.
The fourth phase is the development of the cyber security IT firm marketing plan. Here, we focus heavily on direct outreach initiatives as this is typically the most cost-effective way of onboarding clients that have certain complex cyber security needs. This is complemented by a discussion regarding numerous marketing strategies including both regional and national level, search engine optimization, pay per click marketing, social media ads, the development of podcasts, and video marketing development. Given the level of competition that is experienced by these businesses, it is imperative that numerous online marketing strategies are used in order to create a significant amount of brand name visibility.
As the foundational plans are chapters are completed, we then move into developing the secondary chapters and appendices of the business plan. This includes the creation of a SWOT analysis. As it relates to the strengths of a cyber security IT firm, these businesses are relatively immune from negative changes in the economy. They also produce highly recurring streams of revenue. As it relates to weaknesses, these businesses do face a significant amount of competition as well as facing potential liabilities in the event that there was a catastrophic event. These firms also enjoyed numerous opportunities through ongoing expansion of their marketing campaigns as well as hiring of specialized IT professionals that can render our auditing services. As a relates the threats, this is primarily geared towards competitive issues as well as the potential for having a client experience a breach.
We also conduct an extensive amount of risk analysis specific for cyber security firms as well. This includes an overview of the pre-launch issues that can occur as well as certain specific operating issues that can develop throughout the life of the business.
Now that the business plan is complete, we move into the final chapter which is the executive summary. We always develop this aspect of the cyber security IT firm business plan last so that we can provide a deep overview in a condensed manner for the reader. Here, we hone in on the highlights of the business including its ability to generate recurring streams of revenue, while concurrently discussing how the business will launch its operations and expand.
